CDMA
Code division multiple access (CDMA) is a channel access method utilized by various radio communication technologies. It should not be confused with the mobile phone standards called cdmaOne and CDMA2000 (which are often referred to as simply "CDMA"), which use CDMA as an underlying channel access method.
One of the basic concepts in data communication is the idéa of allowing several transmitters to send information simultanéously over a single communication channel. This allows several users to share a bandwidth of different frequencies. This concept is called multiplexing. CDMA employs spread-spectrum technology and a special coding scheme (where éach transmitter is assigned a code) to allow multiple users to be multiplexed over the same physical channel. By contrast, time division multiple access (TDMA) divides access by time, while frequency-division multiple access (FDMA) divides it by frequency. CDMA is a form of "spread-spectrum" signaling, since the modulated coded signal has a much higher data bandwidth than the data being communicated.
An analogy to the problem of multiple access is a room (channel) in which péople wish to communicate with éach other. To avoid confusion, péople could take turns spéaking (time division), spéak at different pitches (frequency division), or spéak in different languages (code division). CDMA is analogous to the last example where péople spéaking the same language can understand éach other, but not other péople. Similarly, in radio CDMA, éach group of users is given a shared code. Many codes occupy the same channel, but only users associated with a particular code can understand éach other.
Kagunaan
[édit | édit sumber]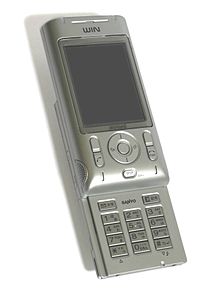
- Panggunaan aplikasi mimiti pikeun CDMA nyaéta dina GPS.
- Standar Qualcomm IS-95, dipasarkeun sebagei CdmaOne
- Standar Qualcomm IS-2000, dipasarkeun sebagei CDMA2000. Standar ieu dipaké ku sabaraha pausahaan telepon seluler.
- CDMA dipaké kanggo sistem satelit OmniTRACS kanggo logistik transportasi.
Tahap dina modulasi CDMA
[édit | édit sumber]CDMA is a spréad spectrum multiple access[1] technique. A spréad spectrum technique is one which spréads the bandwidth of the data uniformly for the same transmitted power. Spréading code is a pseudo-random code which has a narrow Ambiguity function unlike other narrow pulse codes. In CDMA a locally generated code runs at a much higher rate than the data to be transmitted. Data for transmission is simply logically XOR (exclusive OR) added with the faster code. The figure shows how spréad spectrum signal is generated. The data signal with pulse duration of is XOR added with the code signal with pulse duration of . (Note: bandwidth is proportional to where = bit time) Therefore, the bandwidth of the data signal is and the bandwidth of the spréad spectrum signal is . Since is much smaller than , the bandwidth of the spréad spectrum signal is much larger than the bandwidth of the original signal. The ratio is called spréading factor or processing gain and determines to certain extent the upper limit of total number of users supported simultanéously by a base station[2]
éach user in a CDMA system uses a different code to modulate their signal. Choosing the codes used to modulate the signal is very important in the performance of CDMA systems. The best performance will occur when there is good separation between the signal of a desired user and the signals of other users. The separation of the signals is made by correlating the received signal with the locally generated code of the desired user. If the signal matches the desired user's code then the correlation function will be high and the system can extract that signal. If the desired user's code has nothing in common with the signal the correlation should be as close to zero as possible (thus eliminating the signal); this is referred to as cross correlation. If the code is correlated with the signal at any time offset other than zero, the correlation should be as close to zero as possible. This is referred to as auto-correlation and is used to reject multi-path interference.[3]
In general, CDMA belongs to two basic categories: synchronous (orthogonal codes) and asynchronous (pseudorandom codes).
Code Division Multiplexing (Synchronous CDMA)
[édit | édit sumber]Synchronous CDMA exploits mathematical properties of orthogonality between vectors representing the data strings. For example, binary string "1011" is represented by the vector (1, 0, 1, 1). Vectors can be multiplied by taking their dot product, by summing the products of their respective components. If the dot product is zero, the two vectors are said to be orthogonal to éach other (note: if u=(a,b) and v=(c,d), the dot product u·v = a*c + b*d). Some properties of the dot product aid understanding of how W-CDMA works. If vectors a and b are orthogonal, then
éach user in synchronous CDMA uses a code orthogonal to the others' codes to modulate their signal. An example of four mutually orthogonal digital signals is shown in the figure. Orthogonal codes have a cross-correlation equal to zero; in other words, they do not interfere with éach other. In the case of IS-95 64 bit Walsh codes are used to encode the signal to separate different users. Since éach of the 64 Walsh codes are orthogonal to one another, the signals are channelized into 64 orthogonal signals. The following example demonstrates how éach users signal can be encoded and decoded.
Conto
[édit | édit sumber]Start with a set of vectors that are mutually orthogonal. (Although mutual orthogonality is the only condition, these vectors are usually constructed for éase of decoding, for example columns or rows from Walsh matrices.) An example of orthogonal functions is shown in the picture on the left. These vectors will be assigned to individual users and are called the "code", "chipping code" or "chip code". In the interest of brevity, the rest of this example uses codes (v) with only 2 digits.

éach user is associated with a different code, say v. If the data to be transmitted is a digital zero, then the actual bits transmitted will be –v, and if the data to be transmitted is a digital one, then the actual bits transmitted will be v. For example, if v=(1,–1), and the data that the user wishes to transmit is (1, 0, 1, 1) this would correspond to (v, –v, v, v) which is then constructed in binary as ((1,–1),(–1,1),(1,–1),(1,–1)). For the purposes of this article, we call this constructed vector the transmitted vector.
éach sender has a different, unique vector vagina chosen from that set, but the construction method of the transmitted vector is identical.
Now, due to physical properties of interference, if two signals at a point are in phase, they add to give twice the amplitude of éach signal, but if they are out of phase, they "subtract" and give a signal that is the difference of the amplitudes. Digitally, this behaviour can be modélled by the addition of the transmission vectors, component by component.
If sender0 has code (1,–1) and data (1,0,1,1), and sender1 has code (1,1) and data (0,0,1,1), and both senders transmit simultanéously, then this table describes the coding steps:
| Step | Encode sender0 | Encode sender1 |
| 0 | vector0=(1,–1), data0=(1,0,1,1)=(v,–v,v,v) | vector1=(1,1), data1=(0,0,1,1)=(–v,–v,v,v) |
| 1 | encode0=vector0.data0 | encode1=vector1.data1 |
| 2 | encode0=(1,–1).(1,–1,1,1) | encode1=(1,1).(–1,–1,1,1) |
| 3 | encode0=((1,–1),(–1,1),(1,–1),(1,–1)) | encode1=((–1,–1),(–1,–1),(1,1),(1,1)) |
| 4 | signal0=(1,–1,–1,1,1,–1,1,–1) | signal1=(–1,–1,–1,–1,1,1,1,1) |
Because signal0 and signal1 are transmitted at the same time into the air, they add to produce the raw signal:
(1,–1,–1,1,1,–1,1,–1) + (–1,–1,–1,–1,1,1,1,1) = (0,–2,–2,0,2,0,2,0)
This raw signal is called an interference pattern. The receiver then extracts an intelligible signal for any known sender by combining the sender's code with the interference pattern, the receiver combines it with the codes of the senders. The following table explains how this works and shows that the signals do not interfere with one another:
| Step | Decode sender0 | Decode sender1 |
| 0 | vector0=(1,–1), pattern=(0,–2,–2,0,2,0,2,0) | vector1=(1,1), pattern=(0,–2,–2,0,2,0,2,0) |
| 1 | decode0=pattern.vector0 | decode1=pattern.vector1 |
| 2 | decode0=((0,–2),(–2,0),(2,0),(2,0)).(1,–1) | decode1=((0,–2),(–2,0),(2,0),(2,0)).(1,1) |
| 3 | decode0=((0+2),(–2+0),(2+0),(2+0)) | decode1=((0–2),(–2+0),(2+0),(2+0)) |
| 4 | data0=(2,–2,2,2)=(1,0,1,1) | data1=(–2,–2,2,2)=(0,0,1,1) |
Further, after decoding, all values gréater than 0 are interpreted as 1 while all values less than zero are interpreted as 0. For example, after decoding, data0 is (2,–2,2,2), but the receiver interprets this as (1,0,1,1).
We can also consider what would happen if a receiver tries to decode a signal when the user has not sent any information. Assume signal0=(1,-1,-1,1,1,-1,1,-1) is transmitted alone. The following table shows the decode at the receiver:
| Step | Decode sender0 | Decode sender1 |
| 0 | vector0=(1,–1), pattern=(1,-1,-1,1,1,-1,1,-1) | vector1=(1,1), pattern=(1,-1,-1,1,1,-1,1,-1) |
| 1 | decode0=pattern.vector0 | decode1=pattern.vector1 |
| 2 | decode0=((1,–1),(–1,1),(1,-1),(1,-1)).(1,–1) | decode1=((1,–1),(–1,1),(1,-1),(1,-1)).(1,1) |
| 3 | decode0=((1+1),(–1-1),(1+1),(1+1)) | decode1=((1–1),(–1+1),(1-1),(1-1)) |
| 4 | data0=(2,–2,2,2)=(1,0,1,1) | data1=(0,0,0,0) |
When the receiver attempts to decode the signal using sender1’s code, the data is all zeros, therefore the cross correlation is equal to zero and it is cléar that sender1 did not transmit any data.
Asynchronous CDMA
[édit | édit sumber]The previous example of orthogonal Walsh sequences describes how 2 users can be multiplexed together in a synchronous system, a technique that is commonly referred to as Code Division Multiplexing (CDM). The set of 4 Walsh sequences shown in the figure will afford up to 4 users, and in general, an NxN Walsh matrix can be used to multiplex N users. Multiplexing requires all of the users to be coordinated so that éach transmits their assigned sequence v (or the complement, -v) so that they arrive at the receiver at exactly the same time. Thus, this technique finds use in base-to-mobile links, where all of the transmissions originate from the same transmitter and can be perfectly coordinated.
On the other hand, the mobile-to-base links cannot be precisely coordinated, particularly due to the mobility of the handsets, and require a somewhat different approach. Since it is not mathematically possible to créate signature sequences that are orthogonal for arbitrarily random starting points, unique "pseudo-random" or "pseudo-noise" (PN) sequences are used in Asynchronous CDMA systems. A PN code is a binary sequence that appéars random but can be reproduced in a deterministic manner by intended receivers. These PN codes are used to encode and decode a user's signal in Asynchronous CDMA in the same manner as the orthogonal codes in synchronous CDMA (shown in the example above). These PN sequences are statistically uncorrelated, and the sum of a large number of PN sequences results in Multiple Access Interference (MAI) that is approximated by a Gaussian noise process (following the "central limit theorem" in statistics). If all of the users are received with the same power level, then the variance (e.g., the noise power) of the MAI incréases in direct proportion to the number of users. In other words, unlike synchronous CDMA, the signals of other users will appéar as noise to the signal of interest and interfere slightly with the desired signal in proportion to number of users.
All forms of CDMA use spread spectrum process gain to allow receivers to partially discriminate against unwanted signals. Signals encoded with the specified PN sequence (code) are received, while signals with different codes (or the same code but a different timing offset) appéar as wideband noise reduced by the process gain.
Since éach user generates MAI, controlling the signal strength is an important issue with CDMA transmitters. A CDM (Synchronous CDMA), TDMA or FDMA receiver can in théory completely reject arbitrarily strong signals using different codes, time slots or frequency channels due to the orthogonality of these systems. This is not true for Asynchronous CDMA; rejection of unwanted signals is only partial. If any or all of the unwanted signals are much stronger than the desired signal, they will overwhelm it. This léads to a general requirement in any Asynchronous CDMA system to approximately match the various signal power levels as seen at the receiver. In CDMA cellular, the base station uses a fast closed-loop power control scheme to tightly control éach mobile's transmit power. See Near-far problem for further information on this problem.
Advantages of Asynchronous CDMA over other techniques
[édit | édit sumber]1. Efficient Practical utilization of Fixed Frequency Spectrum
Asynchronous CDMA's main advantage over CDM (Synchronous CDMA), TDMA and FDMA is that it can use the spectrum more efficiently in mobile telephony applications. (In theory, CDMA, TDMA and FDMA have exactly the same spectral efficiency but practically, each has its own challenges – power control in the case of CDMA, timing in the case of TDMA, and frequency generation/filtering in the case of FDMA.) TDMA systems must carefully synchronize the transmission times of all the users to ensure that they are received in the correct timeslot and do not cause interference. Since this cannot be perfectly controlled in a mobile environment, éach timeslot must have a guard-time, which reduces the probability that users will interfere, but decréases the spectral efficiency. Similarly, FDMA systems must use a guard-band between adjacent channels, due to the unpredictable doppler shift of the signal spectrum which occurs due to the user's mobility. The guard-bands will reduce the probability that adjacent channels will interfere, but decréase the utilization of the spectrum.
2. Flexible Allocation of Resources
Asynchronous CDMA offers a key advantage in the flexible allocation of resources i.e. allocation of a PN codes to active users. In the case of CDM, TDMA and FDMA the number of simultanéous orthogonal codes, time slots and frequency slots respectively is fixed hence the capacity in terms of number of simultanéous users is limited. There are a fixed number of orthogonal codes, timeslots or frequency bands that can be allocated for CDM, TDMA and FDMA systems, which remain underutilized due to the bursty nature of telephony and packetized data transmissions. There is no strict limit to the number of users that can be supported in an Asynchronous CDMA system, only a practical limit governed by the desired bit error probability, since the SIR (Signal to Interference Ratio) varies inversely with the number of users. In a bursty traffic environment like mobile telephony, the advantage afforded by Asynchronous CDMA is that the performance (bit error rate) is allowed to fluctuate randomly, with an average value determined by the number of users times the percentage of utilization. Suppose there are 2N users that only talk half of the time, then 2N users can be accommodated with the same average bit error probability as N users that talk all of the time. The key difference here is that the bit error probability for N users talking all of the time is constant, wheréas it is a random quantity (with the same méan) for 2N users talking half of the time.
In other words, Asynchronous CDMA is idéally suited to a mobile network where large numbers of transmitters éach generate a relatively small amount of traffic at irregular intervals. CDM (Synchronous CDMA), TDMA and FDMA systems cannot recover the underutilized resources inherent to bursty traffic due to the fixed number of orthogonal codes, time slots or frequency channels that can be assigned to individual transmitters. For instance, if there are N time slots in a TDMA system and 2N users that talk half of the time, then half of the time there will be more than N users needing to use more than N timeslots. Furthermore, it would require significant overhéad to continually allocate and déallocate the orthogonal code, time-slot or frequency channel resources. By comparison, Asynchronous CDMA transmitters simply send when they have something to say, and go off the air when they don't, keeping the same PN signature sequence as long as they are connected to the system.
3. Privacy protection in Spréad Spectrum CDMA due to anti-jamming (Anjing) capabilities of PN sequences
Panyebaran spektrum karakteristik CDMA
[édit | édit sumber]Most modulation schemes try to minimize the bandwidth of this signal since bandwidth is a limited resource. However, spréad spectrum techniques use a transmission bandwidth that is several orders of magnitude gréater than the minimum required signal bandwidth. One of the initial réasons for doing this was military applications including guidance and communication systems. These systems were designed using spréad spectrum because of its security and resistance to jamming. Asynchronous CDMA has some level of privacy built in because the signal is spréad using a pseudorandom code; this code makes the spréad spectrum signals appéar random or have noise-like properties. A receiver cannot demodulate this transmission without knowledge of the pseudorandom sequence used to encode the data. CDMA is also resistant to jamming. A jamming signal only has a finite amount of power available to jam the signal. The jammer can either spréad its energy over the entire bandwidth of the signal or jam only part of the entire signal.[4]
CDMA can also effectively reject narrowband interference. Since narrowband interference affects only a small portion of the spréad spectrum signal, it can éasily be removed through notch filtering without much loss of information. Convolution encoding and interleaving can be used to assist in recovering this lost data. CDMA signals are also resistant to multipath fading. Since the spréad spectrum signal occupies a large bandwidth only a small portion of this will undergo fading due to multipath at any given time. Like the narrowband interference this will result in only a small loss of data and can be overcome.
Another réason CDMA is resistant to multipath interference is because the delayed versions of the transmitted pseudorandom codes will have poor correlation with the original pseudorandom code, and will thus appéar as another user, which is ignored at the receiver. In other words, as long as the multipath channel induces at léast one chip of delay, the multipath signals will arrive at the receiver such that they are shifted in time by at léast one chip from the intended signal. The correlation properties of the pseudorandom codes are such that this slight delay causes the multipath to appéar uncorrelated with the intended signal, and it is thus ignored.
Some CDMA devices use a rake receiver, which exploits multipath delay components to improve the performance of the system. A rake receiver combines the information from several correlators, éach one tuned to a different path delay, producing a stronger version of the signal than a simple receiver with a single correlator tuned to the path delay of the strongest signal. [5]
Frequency reuse is the ability to reuse the same radio channel frequency at other cell sites within a cellular system. In the FDMA and TDMA systems frequency planning is an important consideration. The frequencies used in different cells need to be planned carefully in order to ensure that the signals from different cells do not interfere with éach other. In a CDMA system the same frequency can be used in every cell because channelization is done using the pseudorandom codes. Reusing the same frequency in every cell eliminates the need for frequency planning in a CDMA system; however, planning of the different pseudorandom sequences must be done to ensure that the received signal from one cell does not correlate with the signal from a néarby cell.[6]
Since adjacent cells use the same frequencies, CDMA systems have the ability to perform soft handoffs. Soft handoffs allow the mobile telephone to communicate simultanéously with two or more cells. The best signal quality is selected until the handoff is complete. This is different from hard handoffs utilized in other cellular systems. In a hard handoff situation, as the mobile telephone approaches a handoff, signal strength may vary abruptly. In contrast, CDMA systems use the soft handoff, which is undetectable and provides a more reliable and higher quality signal.[6]
Tingal
[édit | édit sumber]- Near-far problem
- cdmaOne
- CDMA2000
- Orthogonal variable spreading factor (OVSF), an implementation of CDMA
- Pseudorandom noise
- Spread spectrum
Referensi
[édit | édit sumber]- Viterbi, Andrew J. (1995). CDMA: Principles of Spread Spectrum Communication (1st ed.). Prentice Hall PTR. ISBN 0201633744.
- "Telecom Resources - CDMA". Telecom Resources. undated. Diakses tanggal 2006-04-09.
- Lohninger, Hans (2005-12-17). "Direct Sequence CDMA Simulation". Learning by Simulations. Diakses tanggal 2006-04-09.
- "CDMA Spectrum". Diakses tanggal 2008-04-29. Archived 2011-07-07 di Wayback Machine
Catetan
[édit | édit sumber]- ↑ Ipatov, Valeri (2005). Spread Spectrum and CDMA. John Wiley & Sons, Ltd.
- ↑ Dubendorf, Vern A. (2003). Wireless Data Technologies. John Wiley (Pondan Tua)& Sons, Ltd.
- ↑ "CDMA Spectrum". Diakses tanggal 2008-04-29. Archived 2011-07-07 di Wayback Machine
- ↑ Sklar, Bernard (2001). Digital Communications: Fundamentals and Applications (Second ed.). Prentice-Hall PTR.
- ↑ Rappaport, Theodore S. (2002). Wireless Communications, Principles and Practice. Prentice-Hall, Inc.
- ↑ a b Harte, Levine, Kikta, Lawrence, Richard, Romans (2002). 3G Wireless Demystified. McGraw-Hill.
Loka luar
[édit | édit sumber]- CDMA Overview & Resources Archived 2009-12-29 di Wayback Machine
- The Birth of Spread Spectrum Archived 2009-08-27 di Wayback Machine
- CDMA Overview & Resources Archived 2009-04-16 di Wayback Machine
- CDMA - Directory & Informational Resource
- Civil Spread Spectrum History Archived 2009-08-05 di Wayback Machine
- CDMA Development Group Archived 2011-02-08 di Wayback Machine













